
- Boutique Web Development and Hosting Solutions
- Audio/Video Production and Post Production
- Music Instruction
- Songwriting Development / Arranging / Session Tracks
- Publishing
Forthcoming release:
Creamery Station “Walk With Me”
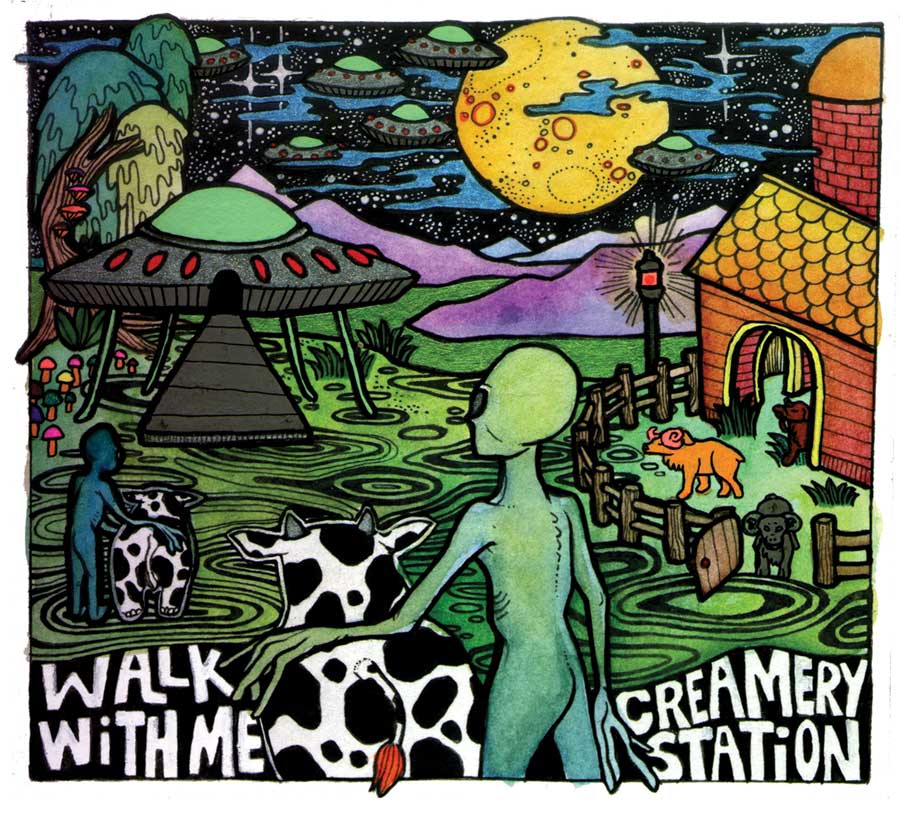
expected release date: July 10, 2020
purchase details coming soon.
Contact TruMedia to discuss your project: